“The best way to explain it is to do it.”
Chapter III. A Caucus-Race and a Long Tale, Alice’s Adventures in Wonderland (1865)”
This quote says a lot. In many cases leadership, as a CISO or similar roles within cyber and information security or in business management, the best way to lead is to explain. And explaining by doing is a lot more powerful than drawing those PowerPoints and strategies. Those are also needed, to set the direction on the map and point out the path for the team and the organization.
As long as there is no execution the value realization equals, close to, zero. I believe in pulling up the sleeves and leading by doing. Instead of just telling others how to do it or what to do, get in there are do it together with the team. Coach your team. Lead them. But at the same time don’t be afraid of getting some dirt under your nails.
There is so much power in “leading by example”, practicing what you preach. You don’t need to be an expert and know everything in detail but show your team that you are there for them. That you provide to the overall strategy by doing, not only thinking or telling others what to do. And if there are other people in the team better suited, more intelligent, and better skilled in certain tasks it’s time to be grateful. Let them take lead in those activities and areas where they are the experts. Let them grow beside you. To lead you on your common journey. So that you both grow as leaders within cyber and information security. As humans and professionals. Coaching and leading is a two-way street.
APPLYING THINGS INTO PRACTICE
After two articles describing the importance of leadership skills, business understanding, and communication skills part 3 will exemplify the application of these skills. Remember, skills are something that can be improved and developed if there is enough motivation and resources provided. Resources often mean sanctioned time for the individual.
Today, knowledge is everywhere. It’s fantastic. If you want to keep learning I can not emphasize enough staying updated, and analytical and surrounding yourself with people who are smarter than you and willing to share their knowledge and experience. And this also goes both ways, share your knowledge and experience with others. Be a provider and be willing to listen to others. Motivation. I don’t think we need to boil into this subject. We all understand this portion. Sometimes it will drop a bit and sometimes it will skyrocket. Anyway, if there is motivation and resources the skills are possible to be gained.
I am, at least according to myself + colleagues + friends + customers, a structured and analytical dude. Something that I find very useful, in my own profession and in my assignments where I have acted as a CISO, is to form a roadmap dividing activities/projects/tasks etcetera into operational, tactical, and strategic categories. This may be something that is totally obvious for most, but many organizations out there, unfortunately, lack this type or similar form of structure. Everything they do, independent of if it is operational, tactical, or strategic thing is put into the same bucket. Nothing wrong in doing so but all activities/projects/tasks etcetera within an organization are not equally weighted or of the same character. Sorting and structuring things into stringent forms provides not only a structure. It also enables us to better develop a long-term plan. Something sustainable to work towards.
Just to make this portion of the article easy, let’s say for example that the following principles apply:
- OPERATIONAL – things are done on a daily/weekly/monthly basis and provide an increased security perspective for the organizations more or less directly. These things can for example be classification of information, data protection, ongoing risk management activities, and security control maintenance. The day-to-day stuff. Some of these things are also, as I see it, related to security hygiene. Nothing fancy, just those things that shall and need to be there.
- TACTICAL – things that are done on a less frequent basis but have a goal to enhance the organization’s security posture within a time frame of, let’s say in this example, approximately 12 months. These things are typically projects conducted over a more stretched period time frame of months or beyond. The value realization is not immediate but is a result of sanctioned resources of work conducted during longer periods of time. These things can for example be the development of a security policy, construction of a risk framework, implementation of security awareness, education of staff members, and third-party risk assessment frameworks.
- STRATEGIC – things that are done within a stretched time frame to enhance the organization’s security posture in the long run. The value realization is estimated to be realized within a time frame of 12-24 months. This, for example, includes re-engineering the information security landscape, establishing security governance, implementing and developing security practices, implementing and development of information classification framework, implementing and developing a risk management framework, and running a security improvement program. These are the things that require more stamina and persistence.
What goes in in the different buckets and the principles applied, in terms of time frames and so forth, will vary between organizations. Above is just an example of how this form of planning can help an organization and the CISO to better visually, verbally, with a pragmatic and structured form present the “security stuff” to the stakeholders (security teams, board, management teams, leaders, and key stakeholders in the business).
The takeaway here is to have a structured form of what is going to be done and how the value realization is approximated to be actualized. This will help you as a CISO to gain an understanding of what is needed to be done and when. The resources needed.
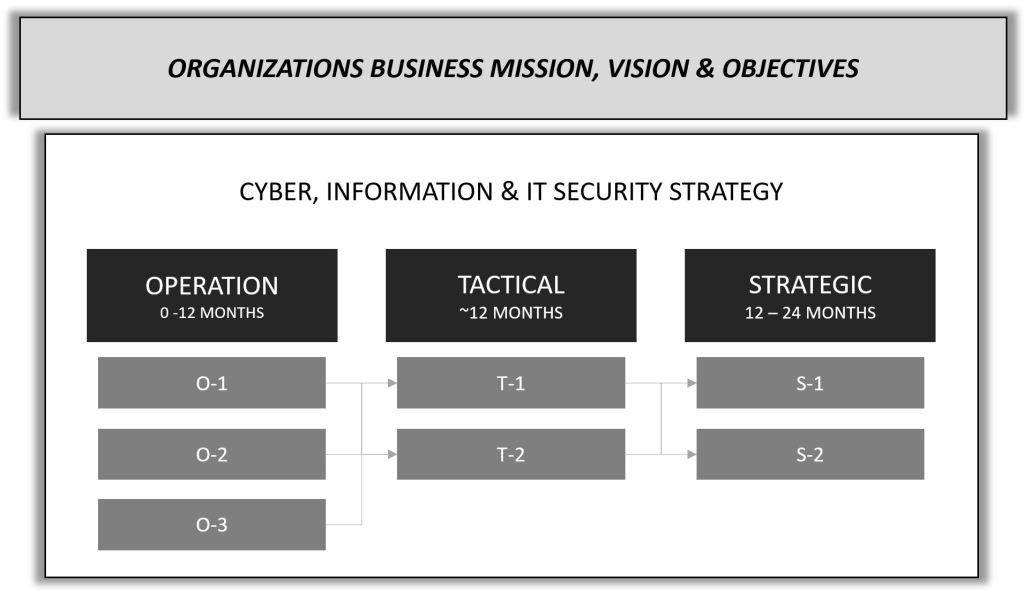
The team you have around you will see the bigger picture and understand which destination is on the horizon. Having a plan, that stretches over a period of time, also creates sustainability. A plan also provides fantastic moments to celebrate the small victories along the road, those milestones.
Forming a plan together with a team also creates a sense of patience. Things take time. Things take resources. Everything cannot be done at the same time and should not be done at the same time. It is rarely seen in any form of a team sport that all plans and activities are conducted at the same time. “Let’s go on attack mode and execute all our offensive strategies at once!”. Nope, that’s not so likely. There is no difference in cyber security. It is a team sport that also needs intelligent planning, plans, and execution.
AND NOW WHAT?
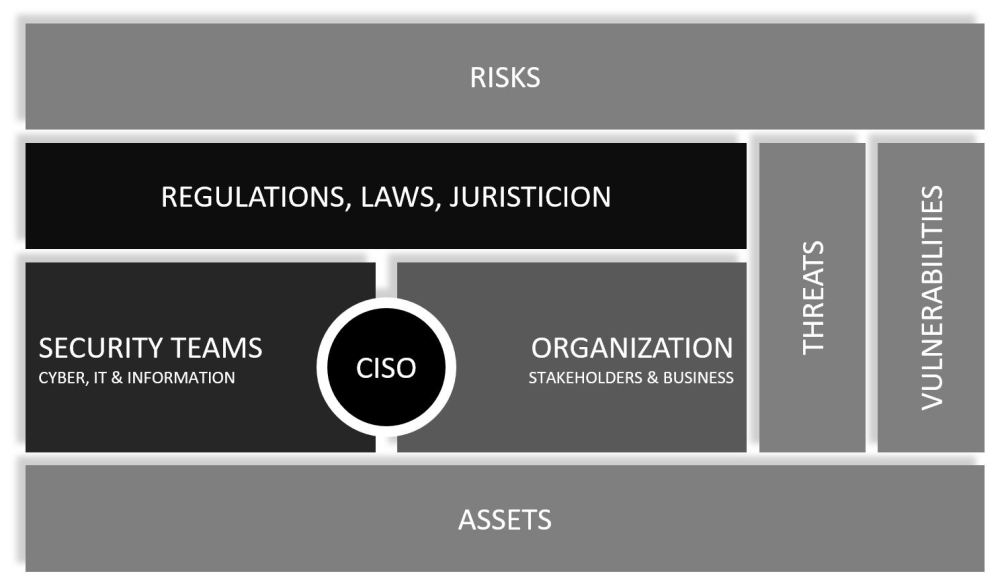
But before the CISO can start to work towards the operational, tactical, and strategic goals outlined the CISO must ensure to have the management support. Yes, the management and leaders in the organization need to stand behind the CISO and support the work.
If the plans are in place but there is no support for them from the upper management and leaders the execution will become troublesome. The classic pitfall of all change management initiatives. If there is no support, it becomes very much of a moment where one bangs the head against the wall. A change is about the people in the organization and the organization as a totality. Communication is key in every form of change. And to have support for a change is king. When support is established, the execution can start and take place.
So, before we as a CISO are going to start and execute the operational, tactical, and strategic plans following, but not limited to, is highly important to make sure is managed:
- Ensure stakeholders have an understanding of the Information, cyber, and IT security plan and how the initiatives/activities/projects etcetera relates to the business strategy.
- When forming and crafting the overall plan for the organization, construct it in such a way that clearly shows how operational, tactical, and strategic initiatives within the information, cyber, and IT security relate to the business strategy.
For example, one of the business goals is to increase time to market and to customers which implies that digital enablement will be on top of the agenda for the coming 36 months. The organization will sanction loads of dollars in the digital strategy and lift and shift several key capabilities to their next level related to “speed to market and customers”.
To support this business initiative the organization will apply a cloud-first strategy, along with other initiatives from other business units. A cloud-first strategy will most certainly lead to the organization will increase its risk exposure related to a third-party perspective, supply chain attacks, miss-configurations etcetera.
For this reason, the CISO can, very easily and pragmatically, explain why third-party risk management (but not limited to) from an information, cyber, and IT security perspective needs to be one of the organization’s strategic goals. There is a clear alignment between the business goal for increasing time to market and to customers with a digital enablement strategy and the cloud-first principles.
To tie things together it makes total sense for the CISO to articulate and present a story for the leadership team(s) and the board about why certain security initiatives need to be sanctioned and conducted. Create the story and tie the things together. This will make things more clear and easier to understand for everyone. Security does not exist or operate in a vacuum; it is there to support the organization.
- When forming and crafting the overall plan for the organization, construct it in such a way that clearly shows how operational, tactical, and strategic initiatives within the information, cyber, and IT security relate to the business strategy.
- Information, Cyber, and IT security is something important for the organization that needs continuous investments to be sanctioned.
- Frame the resources, monetary and humanitarian, that the organization you are helping with Information, Cyber, and IT security as an investment. It shall not be seen as “costs” in my opinion.
Security is an investment to ensure potential negative risks are responded to with adequate treatment options in relation to the organization’s security posture and risk appetite. Fancy wordings but it comes down to very much of those things.
A CISO needs to have adequate resources in place to enable the value realization of the initiatives and plans applicable to the organization. The CISO is not a superhero who can do everything on his own. He is not Batman in Gotham City who has all the toys and tools under or within his cool costume. (It would be cool though, to be Batman. The super-hero-dude. Gadgets are cool…and he has a pretty slick car as well that can change shape and form and do all kinds of epic things.) There needs to be a team. And a team is a composition of people who have time to work together to achieve the desired goals.
Unfortunately, in many organizations, IT and security are still seen as a cost center. I get that to some point. If IT is not the “core” service provided to the customers one can argue that it is a cost or “just” an enabler. But at the same time, digital enablement is not a fluke or something that will fade away.
The transformation and evolutionary process of digital and security are just in the beginning phases. In my opinion, the sooner IT, digital, and security are seen as investments the value realization will increase and be speeded up. “Internet is just hype”. Nope, neither internet nor security is a fluke. That is not the case…and will never be.
- Frame the resources, monetary and humanitarian, that the organization you are helping with Information, Cyber, and IT security as an investment. It shall not be seen as “costs” in my opinion.
- The stakeholders (board, business leaders, and management team(s)) need to help you as a CISO in the realization of the operational, tactical, and strategic goals related to Information, Cyber, and IT security.
- The leaders (formal and informal) in the organization need to help you as a CISO out. Ensure you have the within your corner. Form relationships built on trust. Lead the way and pull up the sleeves and show them how the work is done. Teamwork is key! Inclusiveness is the thing. Develop a team that supports you.
Articulate what type of help you may need from your team. Is it for example communication of security policies, procedures, and guidelines? Propagate security awareness? Leading by example? The power of security will be greatly amplified if the leaders, formal and informal, within the organization are helping you to propagate the messages. The leaders are there to communicate why security is important. The trajectories of a leader’s behavior can be huge when it comes to the positive downstream’s effects. This shall not be underestimated!
Think about it. If the CEO of a big and popular company would stand there, on the frontline and dictating how important information and cyber security are. What would this say about the organization? What would this say about investments within information and cyber security for that organization? What kind of message would this send out? I can think of one specific word. Trust. It would create a feeling of trust. “These guys led by that CEO take security seriously.”. And we are all leaders in one way or another.
A title is great but that doesn’t make one a leader. But those with a great title, have the responsibility to act accordingly. Security is not something about IT technologies. It is something that is about the organization. About the business landscape. It should be there, among the top of the highest priorities for every organization and its agenda. It is those, the board and CEO, who are ultimately responsible for the security. And a CISO is there to help them out. So that we together can make the organization safe by increasing the security posture and alignment towards the risk appetite. Communicate and establish those trustful relationships. Help each other and do it together.
- The leaders (formal and informal) in the organization need to help you as a CISO out. Ensure you have the within your corner. Form relationships built on trust. Lead the way and pull up the sleeves and show them how the work is done. Teamwork is key! Inclusiveness is the thing. Develop a team that supports you.
WHERE TO GO FROM HERE
As spoken about in Part 1 of this series the current security posture of the organization will be one of those things that are going to dictate what should be prioritized. A cyber security assessment can be a good tool to use to better understand where an organization is at, and where they want to go and should be heading. To simplify things, what the operational, tactical, and strategic activities come down to is a composition of the current state, the wanted target state security posture, and the organization’s business goals/strategies.
Personally, I think that it is very good for a CISO to have some sort of hands-on experience in developing, establishing, and implementing some of the things that are included in the crafted plan(s).
This, for example, includes the development of an information security policy, the establishment of security governance, implementation of a risk management framework, conducting of risk assessments, development of an information classification model, project management, and development of a strategy. The list can be made longer, these are just typical examples of things that fall into the realm of cyber and information security. I do not want to say all these things are needed to be mastered or something that is a requirement to be on the CISO’s personal CV BUT it will help the person to better lead the way, lead others in doing the activities or by getting in there and pulling up the sleeves and participating in the production of things. We are back there again, leadership.
But what if there are limited resources? No people around to do the things, develop, and establish the activities in the plan. In this case, the plan(s) may be needed to be downsized to reflect the reality of what is possible to be accomplished. Or the CISO needs to get into the mix and participate in the team and do some of the things necessary himself. And if applicable, gather help from external partners, consultants, and networks. In general,
I think the role as a CISO should be more inclined towards tactical and strategic activities but, personally and based on experience, going in there from time to time and doing the job, leading a project, engaging operationally closer with the teams/stakeholders/project enables understanding and creates trustworthy relationships. I think most of us people gain a stronger trust in those leaders who talk the talk and then walk the walk à “The best way to explain it is to do it.” as mentioned in the prologue. Alice in Wonderland has the answers to many of the CISO questions. One only needs to decipher them accordingly.
STRATEGIC AND TACTICAL THINGS
What are these types of things and why are they even important? It’s a good question to ask and something that I also feel needs to be explained and put in context. The CISO role should, as mentioned in all parts of this series, be driven mainly from a business perspective.
The tactical and strategic things, in terms of activities, should have strong business relation according to my opinion. They should have a strong correlation to how they clearly align towards the business goals and strategies. This for example could include improvement of the organizational security culture by integrating security within business processes supporting the employees, customers, and external parties (partners, vendors etcetera). Or, to enable a stronger security culture within the organization by ensuring relevant measures are cascaded within all levels, horizontals, verticals, and processes. In the best of the world, the organization’s leadership team(s) and the board should be leading lead by example when it comes to security. Dictating the importance of security. Communicating how important it is for the organization. But the CISO can not assume this shall be or is the case.
As a tactical and strategic objective, the CISO needs to in one way or another, educate and enlighten the leadership team(s) within the organization about the importance of security. If you as a CISO do not have the leadership behind you, there is an uphill climb needed to be made. You need to have them in your corner. Tell them the story about security that you have crafted together with your team. Educate them by leading them in the right direction. Be there to support them in decision-making. Listen to the language they speak. Ask them questions. Invite them to the table. Create these relationships. Build trust. Form the plan. And show them how the different things on that plan(s) (Operational, Tactical, and Strategic stuff) aggregate and relates to the business goals. I’m not saying this is easy. I’m not saying this is hard. I’m just saying this is the way forward.
”No, no! The adventures first, explanations take such a dreadful time.
Chapter X. The Lobster-Quadrille, Alice’s Adventures in Wonderland (1865)”
The adventures need to wait. Explanations need to come first. Help your stakeholders within the organization to understand that the time to form a common understanding, if this is not already formed, around why security is important is key before the adventure can start to take place. There are of course quick wins that can be gained in the meanwhile, but security is a marathon, it’s not a sprint. It is not about putting a check in the box and then saying “Ok, we are safe now.”. It doesn’t work that way. There is no vaccine that prohibits bad things from happening or keeps those bad guys out there away. That’s not how it works.
EPILOGUE
Everything needs to start from somewhere. A plan needs to be crafted in some form and sort. The first pencil strokes may be the hardest or most challenging. “Where do I start and how do I start?” is a question I faced a couple of times regarding the subject of how to create plans and strategies.
”I don’t see how he can ever finish if he doesn’t begin.
Chapter IX. The Mock Turtle’s Story, Alice’s Adventures in Wonderland (1865)”
Start with the quick wins maybe? Start there and do those things which build confidence and quickly provide positive effects for the organization’s security posture. Showcase the effects, in terms of how they better secure the business, to your stakeholders. Have a dialogue with the board and leadership team to conduct a security assessment to identify the current and wanted state of the organization’s security posture. From there, form a plan of activities that are prioritized and categorized (with for example operational, tactical, and strategic buckets of activities). Tie the activities and initiatives to business goals and the organizational strategy. Do this with help from key leaders and business units. Craft the story together with your team. Lead when there is a need to lead. Let others lead you when there is a need to be led. Do the things together. Strive for resilience. Increasing protection. Having fun. And help each other. CISO is a team sport.
Lewis Carroll, thank you for the amazing story written about Alice in Wonderland. I truly love it. In so many ways. The quotes, narrative, structure, and characters. It is a legendary English masterpiece novel from 1865. Maybe Alice will say hello again in the future and be a part of my storytelling again. But for now, the CISO story is over. Thank you all for reading, sharing, and liking the CISO series!
Henrik Parkkinen