“According to National Geographic the risk for a human of getting attacked by a shark is 1 in 3.7 million. You’re also more likely to be injured by home improvement tools than by a shark, according to the Florida Museum of Natural History.”
The impact of being attacked by a shark can have lethal consequences. The probability is not that high tough. And I am scared of sharks. At the same time, I think they are cool. The ultimate predator. And when I was a small kid, I remember those Jaws movies. They were epic, at that time and in those ages. I also remember that soundtrack.
<MUSIC>duunnn dunnn… duuuunnnn duun… duuunnnnnnnn dun dun dun dun dun dun dun dun dun dun dunnnnnnnnnnn dunnnn</MUSIC>
A shark only has one real enemy. The orca, killer whale. Orcas are apex predators, which means they’re at the very top of the food chain and they have no predators. Killer whales are some of the largest and most powerful animals in the ocean, and no other predator can challenge them. But at the end of the day, I am more scared of sharks. Luckily, the waters where I swim around do not have sharks.
Today’s article will not be about the animal kingdom, sharks, or killer whales. But what did it (Risk Management) have to do with shark attacks? Or other forms of events that may have a negative impact? This is what today’s article will be about. Risk and management of risk. Today’s article will give an overview and holistic summary of risk management and how it relates to cyber, information, and IT security. What is risk management? Why is it useful? Who can benefit from it? How and when can risk management be used?
I’m not so much about comparing theoretical statements to each other and pointing out which type of theory that has the correct wording, explanation, or dissection of terms. I am a strong believer in theories and science though, but I try to approach things by being pragmatic. Making those scientific practices and theories applicable to the uniqueness of the situation I’m taking on.
My goal with this article is to simplify the Risk Management discipline. I will mix in a little bit of theory here and there but mostly stick to empiric knowledge and my experiences. And I will of course share a little bit about my own thoughts about the subject in an understandable and easy-going tone.
The idea here is not to give a complete outline of what Risk Management is and is not as a totality. For that there are many good books out there…and I have also had the opportunity to conduct a subject matter expert review on one of these. CRISC Review Manual 7th edition. A really great book. And a great certification.
For those who are interested in risk management and the relationship to cyber, information, and IT security I strongly recommend this certification. If you think about investing in the certification, I suggest you to read this article I have written CISM, CISA &CRISC – Which certification to take?

CRISC is provided by ISACA, take a look here at ISACA’s if this sounds interesting.
risk management explained
Personally, I like risk management a lot! Not only as a discipline within my profession but also as a universal tool that can be used in almost any form of situation.
This does not mean that every time I walk across a road, take a swim in the ocean, surf the internet, click a mail, or buy something I pull up the spreadsheet and subjectively make a qualitative assessment of the likelihood and impact of a negative risk. Or that I go through the steps in the process and say to myself;
“Ok, now I’m in the identification stage. Let’s do some inventory and take it from there.”.
For me, risk management is a cognitive tool and discipline. A tool that I use as a “cognitive magic eight ball to better predict future events” (both positive and negative).
Those who have practiced mindfulness for years do not need to continually remind themself day by day to be mindful. It is a mindset. Likewise, I look at risk management. It is a mindset. And there is a stringent process, method, and things that can help a person or organization with becoming or maturing into a more risk-aware attitude and culture.
Risk management becomes the most powerful when it becomes an integrated part of the organization’s culture and employees. It’s not all about having cool heat maps and methods for quantifying things. All those things will not do a lot of effects if the peoples in the organization are not aware of the risk and understand the implication of a negative impact and if they are realized.
And of course, all the fancy risk management tools, heat maps, spreadsheets, methods, and processes will not do much if they are not understood or used. Education and communication are key…once again when it comes to security.
According to ISO 31000 Risk management is the:
“..systematic application of management policies, procedures and practices to the tasks of communication, consultation, establishing the context, identifying, analyzing, evaluating, treating, monitoring and reviewing risk”.
I think this explanation summarizes it well. This explanation, from ISO 31000, will make more and more sense the longer you get into this article. I will get back to things in this definition during this article, but I will not go full-blast theoretical and just propagate what’s said in the textbooks and similar litterateur.
WHAT IS RISK?
The term risk when it comes to security is related to something negative. Risk is not generally something that is negative though but, in this article, and for most scenarios when it comes to security related to cyber, information, and IT security it is something negative.
Cybercrime is the fastest-growing crime, and it is not a fluke. As digitalization becomes deeper in our societies and organizations as more and more business processes and capabilities become digital the attack surface also grows larger from a macro perspective. Almost every organization is more or less a target for a cyber-attack as long as they have a digital footprint. The same statement applies to us as Humans. Everyone is a target of a cyber-attack.
And for the reason that cyber-attacks, against organizations and us as individuals, become more and more advanced, sophisticated, and aggressive risk management also becomes more and more applicable. Risk is everywhere, not only within the cyber and digital context. But organizations and individuals tend to easier forget that there are risks out there. If the internet would be a physical street I would not walk on that street! But we do so every day. And many even without being the least aware of their behavior. Nothing wrong, this is just how it is. The Internet is full of criminals and corruption and you or your organization can be as little as one click away from identity theft, fraud, ransomware, or security breach. I do not like to go with scare tactics, but this is more or less how it is. It is so easy to become a victim, both for an induvial and an organization.
DESCRIPTIONS
There are two descriptions that I think summarize risk well is presented below with a simple text and an illustration for each one.
Description #1
- The summary of the combined impact and likelihood of a negative event occurring.
Description #2
- A threat exploiting a vulnerability that is resulting in negative damage to an asset.

They both make total sense. The first one is a good one to start out with to not complicate things. This is also one of the descriptions found in the most theoretical literature. This is also the explanation that is used in the CRISC exam.
The second description of risk put some other terms into play when speaking about risk from a negative perspective in the security context. The terms I mean are: “Threat“, “Vulnerability“, and “Asset“. These terms are usually found and spoken about in for example security testing, penetration tests, red team engagements, cyber security assessments, and so forth.
I like to combine these two statements which give us the following:
- A Risk is the summary of the combined impact and likelihood of a threat exploiting a vulnerability that is resulting in negative damage to an asset.
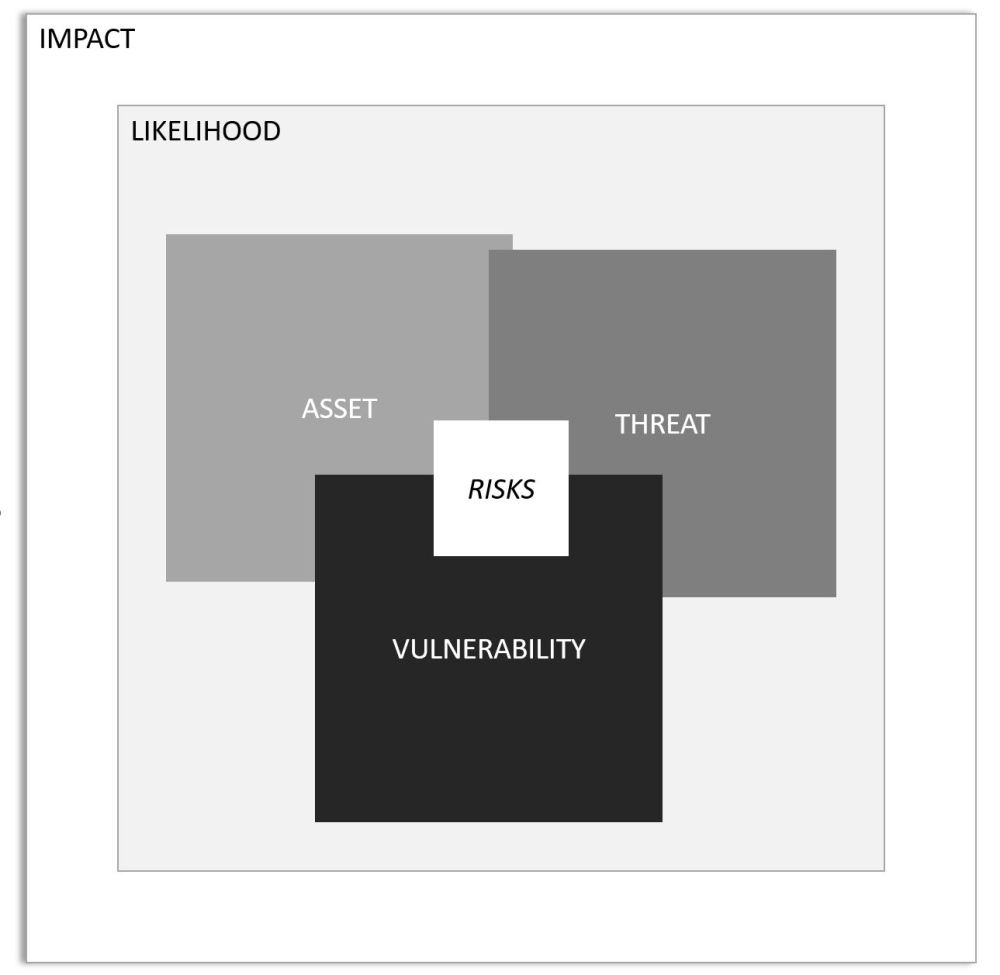
This description gives a summary of all the terms/elements, but it might be something that could be confusing for a first-time reader or student. There are a lot of terms and what they mean and how they relate to each other.
Each term/element (Impact, Likelihood, Assets, Threats, Vulnerabilities, and Risks) all have its place when it comes to Risk Management. What I have noticed though is that these terms are not something that is always clear for everyone when risks are assessed, analyzed, or in other forms managed.
Before all these terms/elements are used make sure to explain what the differences are and what they make up in risk.
Below is a short description of each term.
- Impact – The magnitude of the negative event from a threat exploiting a vulnerability.
- Likelihood – The probability of something, i.e. an event, happening.
- Asset – Something of either tangible or intangible value that is work protecting. For example, humans, data, information, intellectual properties, reputation, business processes, and finances.
- Threat – A potential cause of an unwanted incident or anything that is capable of acting against an asset in a manner that can result in a negative impact or consequence. A threat is in general something that cannot be controlled. For example, a hurricane, geo-political events, or cyber criminals. When there is a human behind a threat, they are in most cases driven by two factors: skill and motivation. Skill is the knowledge they possess. Motivation is in most cases related to financial and monetary aspects.
- Vulnerability – a weakness in the design, implementation, operation, or internal control of an asset (system, process, infrastructure, human) that could expose the asset to adverse threats or threat events. A vulnerability is in general something that can be controlled, i.e. mitigated. For example, a security update is missing on a system, a bug is identified in the software, and the employees lack of security awareness training.
- Risk – see explanation above.
It is not always needful to identify the threat and vulnerability when conducting a risk assessment. I strongly recommend that this is done though. The reason for this is due to that:
- if more information is identified and taken into consideration when a risk assessment and analysis is conducted it will help to ensure adequate measures are possible to be applied in relation to the risk.
- Example more accurate response & treatment options, i.e. acceptance, avoidance, transfer, mitigation of risk.
- Establishment or implementation of additional security controls.
- Establishment or implementation of additional security controls.
- Example increased and more accurate monitoring & reporting of risk, i.e. KPI, PI, KRI, metrics.
- Establishment of threat intelligence and detective controls to monitor changes in the external threat landscape.
- Example more accurate response & treatment options, i.e. acceptance, avoidance, transfer, mitigation of risk.
The more information that can be gained when risk is assessed and to be analyzed, the better! It is as simple as that. Strive to gain as much information as possible during each identification and assessment. And as risks may change over time make sure to conduct the assessments and analysis on a continual and periodic basis.
THE RISK MANAGEMENT DISCIPLINE
Risk Management shall be seen as the discipline for how risk is managed as a totality with the help of systematic and methodical processes, procedures, and guidelines.
Examples:
- Process – implies a structured way of describing how a risk assessment is to be conducted.
- Procedure – implies the description of how risk analysis is conducted.
- Guidelines – implies guiding principles helping the risk practitioner out with activities related to identification, assessment, treatment, and monitoring of risk.
It is common that Risk Management, Assessment, and Analysis get mixed up. As I will use these terms on a regular basis in future articles here on my website, I will provide a simple explanation below:
- Risk Management [Discipline] – The discipline for how risk is managed as a totality and with the help of systematic and methodical processes, procedures, and guidelines.
- Risk Assessment [Process] – The process for Identification, Analysis, Treatment & Response, Monitoring & Reporting of risk.
- Risk Analysis [Phase] – A phase in the Risk Assessment process.
Think about it this way if you need to remind yourself about the interrelationship:
“Within the Risk Management discipline, the Risk Assessment process exists. Within the Risk Assessment Process, the Risk Analysis phase exists.”
Below figure is a visualization and holistic representation of the discipline Risk Management process from a general perspective and how the different steps in the overall process fit together.
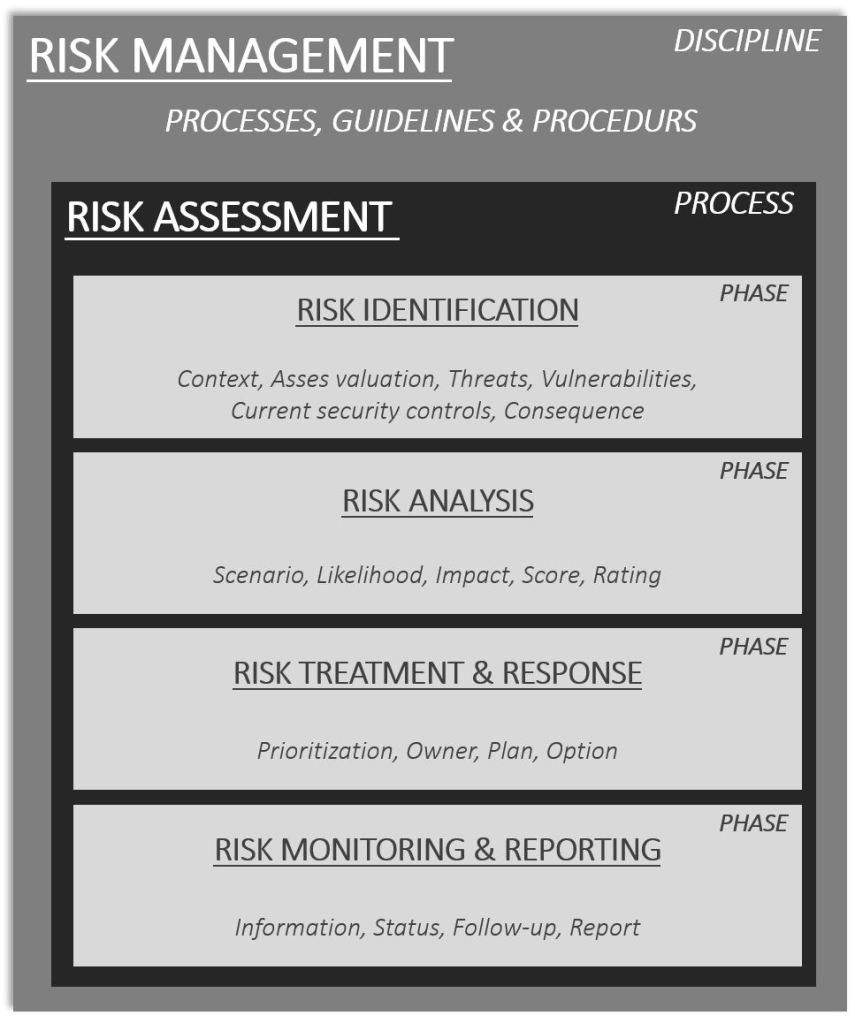
The illustration is an example of the Risk Management discipline. It may vary between frameworks, standards, and how organizations implement it but in general, it contains more or less the pieces in the illustration.
when shall risk management be used?
Apply the power of risk management in all scenarios when found applicable. And I can promise you that those are many! When it comes to security there are loads of scenarios where risk management will be beneficial.
For example:
- Procurement of new systems, for example investment in cloud services, on-prem services etcetera
- Introduction of new regulations and compliance requirements
- Classification of information and systems
- Evaluation and assessment of current security controls
- Establishment of new technologies
- Assessment of emerging technologies
- Assessment of decommissions of existing technologies, information systems, business processes etcetera
- Merges and acquisitions
My recommendation around When in time to apply risk management and conduct an assessment is “As soon as possible and continually when new information becomes available.”. Risks are dynamic and change over time. A risk identified during a time will be rated based on the information available during that period, but the severity of the risk may change (go up or down) as new information becomes available.
In almost every case it will be the best option to conduct a risk assessment as soon as possible. If for example, you would do procurement of a new cloud service and a risk assessment is not made during the procurement, pre-study phase or prior to the implementation what would a risk assessment provide when the cloud service is already implemented?
The risks identified post-implementation, when the cloud service is in production, might already have resulted in a legislative or regulatory compliance breach when it comes to data management. The damage is already made. A breach has already taken place. Ok, now there is a possibility to do something about it as awareness has been gained but this is not how it should be done. This is the wrong way.
Unfortunately, this scenario is a classic one for many organizations that invest in cloud services. There is no risk assessment conducted prior to the investment and establishment. Or an “unformal” risk assessment is conducted post-implementation, something like this: “Guys, we breached <insert security requirement(s)>! How are we going to fix this???”. Accountability for security does not stop existing just because the data/information is transferred to a cloud service. The organization that owns the data/information is still accountable for its security. It can NOT be outsourced.
PERSONAL EXPERIENCE of risk management
From my personal experience when and looking back, to those days when the majority of the work I did was on a hands-on technical level, a better and deeper understanding of the risk management discipline would have helped me in my profession.
It would have been enough for me in the early days of my career to understanding how to conduct a “mini risk assessment”. This was nothing I learned from or during my education in IT. Maybe this is something that has shifted, that this is something that is more or less mandatory and included in all forms of IT education programs. I really hope it is, risk is everywhere, and understanding it will create more awareness of risk, threats, and vulnerabilities that exist in the security and IT landscape.
I will take an example here from security-land, a security health check/assessment, and how Risk Management could provide added value. This statement and example are an aggerated view of what I have seen in the real world, and how many of these reports and results have been presented and crafted. This statement goes hand in hand with many technical projects within security, infrastructure, cloud, and so forth. This is nothing unique for us, security people. Why I am using this example, is because I am in the security realm myself and see this as an opportunity to share my experiences of how improvements can be made.
An organization is assigning a consultancy firm to conduct a security health check of an information system. The security health check contains two objectives, a review of the information system and the supplier.
The results from the security health check are collected in a report and presented in a long list of vulnerabilities and risks. The results from the assignment and report are presented with the help of a PowerPoint and a PDF format that is handed over to the customer. Those in the customer’s organization who have an ok technical understanding get a grip of the severity and urgency around some of the recommended mitigating actions. The consultancy company articulated why certain findings were more critical compared to others and also marked them as “High Risk”. Those who have a less technical understanding of the customer’s organization are feeling like they are looking at an advanced and complicated mathematical equation. Ok, so the question is two-folded:
- Can the results be explained in a simpler way and language? Something more universally understandable?
- Shall those persons with less technical understanding be able to and even read that sort of report?
The answers are, Yes and Yes. I think that reports of this form can easily be improved if they are coupled with a simple risk assessment and analysis. If there is room to conduct the risk assessment and analysis together with the customer, the effects will become even better.

A risk assessment together with the customer will also provide an opportunity for each side, the customer and consultancy company, to better understand the application of the risks, threats, and vulnerabilities. For example:
- How have similar risks identified been actualized historically?
- How are similar risks managed today?
- Who is the potential owner of the identified risks?
- How can the identified risks be monitored?
- What forms of response and treatment options are available and applicable to the identified risks?
- And the list goes on…
And I strongly recommend, in the report and presentation, to use visuals and figures. Here that heatmap makes total sense. And if the risks have been rated together with the customer it makes even more sense. The audience and participants now have a visual illustration of where on that heatmap the risks are scored.
The visual effect will provide pragmatic understanding for the customer to get a feeling of the differences between a “risk” and a “risk” now when they are presented with a matrix, heatmap, color coding, traffic lights, or similar.
If the consultancy company that conducts the security health check even can use the organization’s own risk management framework the results will be even easier to understand for the customer. And is this not what it is all about? To make the customer aware of the identified vulnerabilities, threats, and risks? The customer’s organization will better understand how the risk is rated and assessed. How the method for rating the risks is crafted?
This will of course generate a bit higher cost for the assignment as such that the consultancy company conducting the security health check will also need to be introduced and educated in the risk management framework. What is a risk according to the customer’s risk management framework? What is a threat? What is a vulnerability? What is the difference in the impact levels? What are low, medium, and high risks? Are there certain metrics that need to be taken into consideration during the assessment? But this should not be something that takes more than 2-4 hours. And this amount of time, 2-4 hours, is usually a piss in the ocean of the total budget….and it is really the smallest amount of investment in comparison with the cost of a security breach. I understand that for a small organization with a tight budget every hour adds up to their already packed budget.
Organizations out there, pay those few extra hours to make sure the investment of the security health check or other forms of security testing is getting the correct resources they deserve. It is an investment. If you go in on a health control to the doctor, it is unwise to say: “Don’t put so much time in those blood sample analyses, I’m quite fit you know! I was a former high school long distance runner-champ!”.
And just to make sure that no one out there gets offended. I do not generalize and say this is the case in every security assignment, but I have been around the block for a while and got my hands on a couple of reports. The above is just a way for how the message and findings can be better improved. How a better value can be generated for both the customer and those conducting the assignment?
And think about it, if the firm who conducts the assignment also gets to understand how and what risk is at a certain organization, I can bet that it will MOST certainly generate a higher return on the made investment. They will better understand the organization from a risk management perspective and can takes this into the consideration when compiling the final report. Or in their next engagement for the company.
I have heard some organizations saying “We shall not educate external companies we hire for assignments like this. They should be the experts and already know risk management.”. Everything in this sentence is wrong. Everything. There are very few service providers who share this as a core value and want to do business with an organization who have this mentality. And this goes the other way around as well. Service providers who are not willing to educate or properly engage in a partnership with a customer will not be long-lasting in the game either. A two-way street, between a customer and a service provider. And security is a team effort. Do the things together, and it becomes more fun and sustainable for both parties.
Create that relationship and partnership between each other. The opponent is not the service providers or the customer’s organization. The opponent is the bad guy out there in cyberspace who has as motivation to do bad things. They are those who benefit from a political war between the service provider and the customer, no one else. Educate each other and make sure both of you share the same view. I have been taking on security roles on both sides of the game, the customer and service provider’s side. The approach I have used every single time boils down to –> Teamwork. Do it together.
WHERE TO GO FROM HERE?
I have said it before. Start where you and your organization are right now. If you are at the lower end of the maturity scale, then start with the easy things. Start to talk about risk. Start with assessing risk by only applying an Impact and a Likelihood. Record the risk in a register. Expand the register to contain threats, vulnerabilities, and assets, and educate your team members and organization about what these terms mean.
It is also wise to investigate if there is something related to risk management established within the organization. Reuse what has already been used and crafted. Do not invent new things right the way. If you want to jumpstart, ask google and take inspiration from already known standards and frameworks. NIST RFM, NIST CSF, ISO 31000, ISACA IT Risk Resources. There are tons. Don’t limit yourself and your organization to not looking outside of your own kingdom.
If you and your organization have come a bit on the journey, advancing in the discipline of risk management, and seeking how to take the next step in your maturity curve I would suggest you reach out to your network.
And the same thing applies here, if you are “stuck” at some point, ask others how they would have done. There is nothing wrong with asking for help!
“We are stuck here and cannot get engagement from the project management and enterprise architecture office teams! They do not buy in on this new cyber security risk management stuff! How and what should we do now?”.
This is a real-case scenario, by the way, call it a blame game or unwillingness or a battle of egos. It doesn’t matter that much what we call it, but this is not the last time something like this takes place in the corporate world. In security-land. Anyway, the situation got sorted out. And the solution you might want to ask me about. Short answer: communication and education. I made sure all parts of the team understand why it is important that we as an organization work systematically, periodically, and with an intelligent method with risk related to cyber, information, and IT security.
And some last words of wisdom. Adjust and adopt the risk management discipline according to your own requirements and the needs of the organization. Just because a theory says this and that or another organization around you or in your network does in a certain way you are still allowed to follow the path that is right for your own organization.

If you are getting stuck, get some help and external perspectives. In some cases that is enough, in other cases, there is a need for someone to be there and coach, guide and help out with more practical stuff. Strive to create something that is sustainable and how you and your organization can work with risk over time. It shall be something that becomes a part of the culture, this is the end game. But this is not something that happens over a night. It is not a binary switch or digital bit that you just enable in the organization. If it would have been that easy things would look a bit different.
If you found this article interesting and want to learn more about Risk Management, Risk Assessment, Risk Analysis check out this article The Risk Assessment Process & Risk Analysis Phase Explained.
Go forward. Education. Communication. Listen to each other. Share thoughts. Do intelligent things. Contemplate. Be humble. Openminded. Do it as a team. Together. Risks are everywhere.
Henrik Parkkinen