The focus in this article will mainly be on the Risk Assessment Process and the Identification phase. I will go through what they contain and the elements within them.
If you are new to Risk Management, I recommend you to read this article What is Risk Management.
This illustration is a summarized view of Risk Management and the Risk Assessment process.
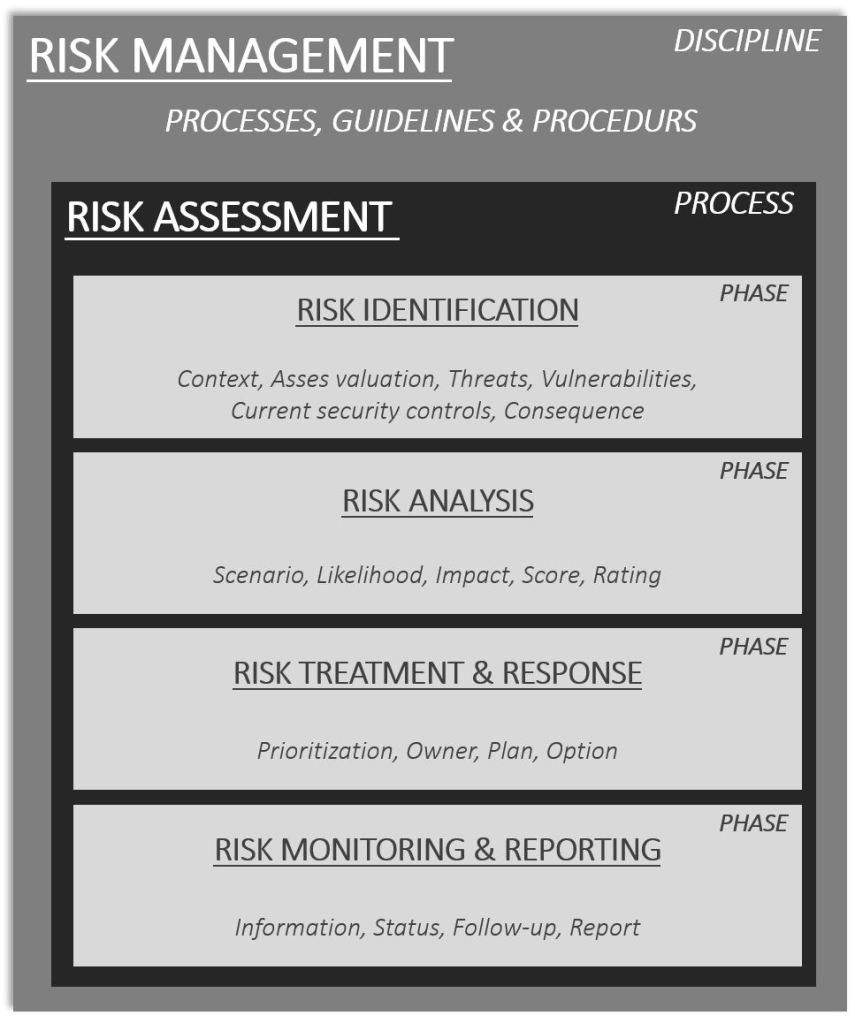
The illustration is an example of the Risk Management discipline. It may vary between frameworks, standards, and how organizations implement it but in general, it contains more or less the pieces in the illustration.
RISK ASSESSMENT
A Risk Assessment consists of phases, in general, these phases are Identification, Analysis, Treatment & Response, Monitoring & Reporting.
The Identification phase has a goal to identify:
- Assets
- Threats
- Vulnerabilities
- Security controls
- Consequences
The Analysis phase has a goal to analyze:
- Risk(s)
- Scenario
- Likelihood
- Impact
- Score
- Rating
The Treatment & Response phase has a goal to decide on:
- Prioritization
- Owner
- Plan
- Option(s)
The Monitoring & Reporting phase has a goal to manage:
- Information
- Status
- Follow-up
- Reporting
There is no right or wrong to how many or which activities that are included in each phase. Those mentioned above are common activities conducted in each phase. Each organization will though choose more or less between which activities they conduct.
It is common to see that organizations tend to skip the Identification, Treatment & Response, Monitoring & Reporting phases. Many jump directly into the Analysis phase when a risk is identified and into the scoring, i.e. estimation of likelihood and impact. There is nothing wrong with doing so. In some cases, the other phases are not needed or relevant.
This can for example be true when an operational change is going to be conducted. There are no actual threats or vulnerabilities that need to be contemplated. The value realization from a risk assessment of the change is gained from analyzing the likelihood and impact to gain an understanding and form a plan. How to roll back the change or how to mitigate if the sh*t hits the fan.
When it comes to security risks, I highly recommend conducting all phases; Identification, Analysis, Treatment & Response, Monitoring & Reporting. The reason for this is due to Threats and Vulnerabilities are elements of a Security Risk. And a risk is dynamic which means that it changes over time. And so do threats. A vulnerability might stay somewhat static but may also change.
A security risk is dynamic and changes over time. A change can take place very fast, for example within the same day.

It is common that Risk Management, Assessment, and Analysis get mixed up. As I will use these terms on a regular basis in future articles here on my website, I will provide a simple explanation below:
- Risk Management [Discipline] – The discipline for how risk is managed as a totality and with the help of systematic and methodical processes, procedures, and guidelines.
- Risk Assessment [Process] – The process for Identification, Analysis, Treatment & Response, Monitoring & Reporting of risk.
- Risk Analysis [Phase] – A phase in the Risk Assessment process.
Think about it this way if you need to remind yourself about the interrelationship:
“Within the Risk Management discipline, the Risk Assessment process exists. Within the Risk Assessment Process, the Risk Analysis phase exists.”
The Risk Assessment process related to security risk(s) shall not be seen as a linear process. The activities shall though be conducted in a systematic approach, phase by phase. But as soon as new information becomes available during later phases that are relevant to earlier phases in the process and for the risk, those previous phases shall be revisited. As mentioned before, risk is dynamic. And new information might be identified or become available in later phases that were not accessible in the initial phases.
This is for example true of cyber-attacks and threats. As more threat intelligence is gained that correlates to a certain risk a new risk analysis might be needed to be conducted. The likelihood and impact may for example be needed to be contemplated once again which can have downstream effects on if additional security controls or other response options shall be applied.
IDENTIFICATION phase
As soon as a risk has been identified it shall be recorded and stored in the organization’s risk register. A risk register will usually take on different forms between organizations. I have seen and worked with dedicated risk management systems to spreadsheets.
I personally believe it is more important to start recording risks instead of spending time evaluating tools and systems. This is explicitly true is you are starting out with risk management.
Start with learning the discipline and process first. As maturity grows so do the requirements. For a larger organization, a dedicated system may be a “shall” requirement though. One of the reasons for this can be that the risk management framework and system need to provide capabilities both to stakeholders inside and outside the organization.
ASSETS
The Identification phase has a goal to identify the assets related to the risk and rate the value of the asset in relation to the organization. Assets valuation can be conducted with the help of several methods. Three of the most common are:
- Qualitative valuation
- Quantitative valuation
- Semi-quantitative valuation
A qualitative valuation is based on subjective input, mainly provided by experts who understand the value of the asset. The valuation method can utilize a scale or rank. Such as example 1 – 4 or a scale of low, medium, or high.
A quantitative valuation is based on objective input, mainly based on monetary calculations. The valuation can be based on for example net present value, replacement cost, and so forth.
Semi-quantitative valuation is based on both subjective and objective input. A subjective scale is combined with monetary calculations. The method that is used will vary. It will depend on what is applicable and if there is data and information available to support the methodology. If for example there are no cost calculations or monetary figures available this method will not provide any value. In most the cases, there is a financial unit within the organization that hopefully can provide insight and guidance if a quantitative valuation method is preferred to be used. Personally, I prefer to use quantitative methods due to that these reduce subjective input and are generally more understandable by a wider audience in the organization
THREATS
During the identification phase threats are identified and inventoried. Threats come in different forms and will vary between organizations. This is for example due to markets, industries, assets, geopolitics, location, a country the organization operates in.
Questions to contemplate are:
- What are the threats related to this risk?
- Do they come from outside of the organization or do they come from the inside of the organization?
- Are there any environmental threats we need to contemplate?
- Are there special characteristics for the threat related to the risk?
- Are the threats intentional, unintentional, or accidental?
VULNERABILITIES
As a part of the identification phase vulnerabilities are to be identified. This can be a result of the inventory of the currently implemented security controls. Are there any security controls missing that increase the attack surface? Multi-factor authentication is for example not implemented for an application that is accessible from the internet. It is common that vulnerabilities are mostly thought about as something that is technical or related to the technological aspects of security. Do not forget to include the Humans and Processes when analyzing vulnerabilities.
Some good questions to contemplate during the identification phase are:
- Do we have an adequate process in place that support our technologies and make sure they are resilient?
- Do make sure our employees in our organization are educated and trained in security awareness?
- Do we provide our employees with adequate security knowledge periodically?
CONSEQUENCE
During the Identification phase, the potential consequences of the risk shall be contemplated. Ask the question, to the participants in the risk assessment:
“What will happen if the risk is actualized?”
This question can be obvious for some to answer straight up but might for others take time. Have patience and let the participants contemplate the consequences. If you are facilitating the risk assessment process and “have the answer” I recommend you not put it out directly. Facilitate the dialogue and discussion. Lead the participants in the right direction. Coach them on how to find that pathway that leads them closer to the consequence. The key here is to facilitate, lead and coach. It is not about providing the right answers and being the expert.
It happens from time to time that the person who facilitates the risk assessment process also might be the subject matter expert in the subject. This has happened to me several times. In these cases, I try primarily to do what I am just told. Facilitate, lead and coach the team and participants. If I notice that we get stuck, I throw in an:
“I get the feeling of that we are a bit stuck in the thought process. Would you guys be ok, or would you like me to share my thought process?”
Usually, this flies very well and much better compared to if I would provide my thoughts and “the answer” to the consequence straight up. And I this is done, if “the answer” is put out there, without the team and participants even having a chance to contemplate the consequence less knowledge is gained. Risk management is a cognitive tool and skill. It is something that can be trained. Let the team and participants train. Be the coach. This is how I successfully have educated and coached organizations in Risk Management and within the Risk Assessment process. Strive to be the coach.
SECURITY CONTROLS
In the identification phase, it is highly recommended to conduct an inventory and identification of the current security controls implemented. But this is not something that is always done. According to my experience, this is something that is done less often by those who are on the lower maturity scale of Risk Management.
GENERAL RULE
A general rule, that I personally stick to, is that the identification phase should collect as much data and information as possible. The more data and information that is available will be beneficial in further phases in the Risk Assessment. It will become easier and more effective to conduct an analysis the more data and information that is available.
DATA AND INFORMATION GATHERING
The data and information gathering process and methods during the Identification phase will vary. It is common that a combination of both manual and automatic procedures and methods to be applied. But it all also depends on the risk and within the context, it exists.
Emerging risks for example, are risks that in general have very little data and information that leads to their negative impact are not fully understood, which is something else compared to an understandable risk. An understandable risk can for example be a security incident that has occurred in the past. There is data stored in the incident management system, lessons learned, knowledge systems etcetera.
A risk that is closely connected to the business environment, such as example a critical business process in the organization, may need data and information gathering through interviews with business stakeholders.
It is common that data and information need to be collected from several sources and with the help of several different methods.
Examples of useful data and information that are helpful in the Identification phase are:
- Historical security incidents
- Security incidents and events
- Cyber threat intelligence
- Security and audit logs
- Threat hunting data
As the data and information are gathered, from different sources, they may need to be aggregated, correlated, and processed. But this is also something that is highly dependent on the risk and the context in which it exists. If the risk is complex in terms that it spans several information systems and business processes the correlation exercise may need participation from both IT teams, business stakeholders, and senior management. There is no given answer for how this exercise is conducted, it depends. This is the true answer.
The risk Identification phase can contain several persons and I do recommend, in one way or another, engaging with as many persons as possible during this phase who has valuable input. If the facilitation becomes a challenge a good idea can be to send out a survey or form questions directed to the stakeholders from where data and information need to be collected. Generally, it can be challenging to gain attention from the senior management and executives in this phase but at the same time, they may not be needed during this phase. The metrics, KPIs, figures, and others are usually delegated to others who are directly reporting to these positions. Target those persons first. Engage with them and explain to them what you need and how they can help you. Organize your questions and thoughts in advance, this saves time for everyone.
I have conducted risk assessments where only one person, besides myself, has participated. I have conducted risk assessments where a larger crowd (20 – 25) people) participated. I do not recommend conducting risk assessments with a larger crowd. Those tend to become more challenging to facilitate and organize. It can also be challenging from a “scoring” and “rating” perspective if a qualitative risk analysis technique is used. Qualitative risk analysis is based on subjective opinions, experience, and intuition. Quantitative risk analysis is based on objective metrics, such as quantifiable data and figures. I will come back to this subject in the Analysis phase and speak more about facilitation and analysis techniques.
RecommendationS
During the Identification phase, strive to collect as much relevant data and information as possible.
I strongly recommend every organization conduct all the phases included in the Risk Assessment process when security risks are assessed.
I strongly recommend every organization conduct an inventory and identification of the current security controls implemented when conducting a Risk Assessment. This is best done during the Identification phase.
Do not forget to conduct an inventory to identify if there are potential vulnerabilities related to Processes and Humans in relation to the risk that is assessed.
Start easy and progress to more advanced techniques and methods for how to identify risk as you mature in the discipline of Risk Management and the Risk Assessment process. It is more important to start out to conduct Risk Assessments for security risks in comparison to doing nothing. This is an instant win, a low-hanging fruit as they say.
EPILOGUE
“…risk is everywhere and we all do take risk everyday, knowingly or unknowingly.”
Ernest Agyemang Yeboah
That’s how it is, independent if we like it or not. Risk is everywhere. An important subject, closely related to security and a part of life. It is everywhere.
Henrik Parkkinen