WHAT IS THE CIA TRIAD?
History first. And this is what I have come around regarding historical smaller findings around the topic of how the CIA triad became a thing.
The acronym, CIA within Information Security, stands for Confidentiality, Integrity, and Availability which are three common perspectives of security.
The CIA triad is a well-known concept that can be traced back 1976 to in the U.S Air Force where the “C” (Confidently) was used. The “I” (Integrity) became a thing somewhere around 1986 when a special focus on data correctness became a subject. The “A” (Availability) is said to have some relations to the virus Morrison Worm that had devastating effects on thousands of major UNIX machines and the internet.
The CIA triads is a concept still used in the Information Security domain for protecting information. It is not clear when the CIA became a concept but guesstimates on the internetz trace it back to 1998.
When I first encountered the CIA triad a couple of years into my professional career. Think it was in 2004 when I was given an Information Security policy of around 70 pages. There it was the CIA triad and an explanation of what the different letters meant.
The CIA triad can many times be found as an integral part of an information security policy. It is not, according to my opinion, necessary that it must be included and visualized but the policy as such should take the three perspectives into consideration.
the perspectives explained
The three different perspectives of the CIA triad, are summarized according to the following explanations below:
Confidentiality
Implies maintaining the data/information inaccessible and not made available or disclosed to unauthorized organizations or individuals.

Damage to the confidentiality of the data or information may be caused by:
- Loss
- Leakage
- Theft
- Exfiltration
- Malfunctioning information systems
- Misconfiguration of access controls
- or by other harmful events conducted by authorized or unauthorized organizations or individuals.
Examples of security controls related to confidentiality are:
- Authentication
- Access controls
- + other forms of security controls that can be used to restrict access to data and information.
Examples of scenarios that may result in damage made to Confidentiality are:
- Leakage of sensitive information or data
- Leakage of credentials, passwords, usernames, or similar secrets
- Accidentally leaking data or information
- Exfiltration of data or information
Integrity
Implies maintaining and assuring the accuracy and completeness of the data and information.

Damage to the integrity of data or information may be caused by:
- Unauthorized changes or modifications
- Accidental changes or modifications or changes
- Misconfiguration of information systems and software
- Intentional changes or modifications
- Malfunction of information systems and software
- or by other harmful events altering the completeness or accuracy of the data/information, conducted by authorized or unauthorized organizations or individuals.
Examples of security controls related to Integrity are:
- Encryption
- Signing
- Checksums
- Hashes
- + other forms of security controls that can be used to ensure the data and information have not been changed.
Examples of scenarios that may result in damage made to the Integrity are:
- Manipulation of data or information
- Deciphering encrypted data or information
- Tampering or damaging the correctness or accuracy of digital transactions
Availability
Implies maintaining and assuring the availability of the data and information and the delivery methods, communication channels, and connectivity that is used to access it.

Damage to the availability of the data or information may be caused by:
- Unavailability
- Denial
- Disruption
- Misconfiguration of information systems
- Malfunctioning information systems
- or by other harmful events conducted by authorized or unauthorized organizations or individuals.
Examples of security controls related to Availability are:
- High Availability solutions
- Clusters
- Load balancing
- + other forms of security controls that can be used to ensure the availability, of the system, storing or, the data and information are maintained.
An example of damage made to Availability can be caused by:
- Denial of service attacks against an organization, service, information systems
- The high availability solution fails
- Electrical power failure of equipment
For each perspective in the CIA triad, the damage to an asset can be a result of intentional or unintentional actions due to human errors, mistakes, deficiencies related to technologies, environmental, accidents, or harmful events conducted by adversarial threat actors.
The threat can potentially come from the outside of the organization or from the inside. Threats are those things that cannot be controlled. They are mainly driven by motivation and skill when there is a human actor behind the steering wheel.
ANECDOTE
I have experienced that the perspective which often is most challenging and difficult for an audience/stakeholder to grasp is Integrity. One of the reasons behind this is because the Integrity perspective is not something that is broadly used or that is applicable on a wide scale in the everyday life or in job roles.
When analogies or practical scenarios around Integrity are put into context around data and information encryption it becomes somewhat more understandable and easier to relate to. But encryption of data and information (such as for example emails, files, folders etcetera) is not either something that the everyday person may even be aware of or even have a practical experience of. Manually conducting encryption of a digital asset is not something everyone can relate to either and this is especially applicable for those who have less technical knowledge, understanding, and interest.
Encryption is actually very widely used in the everyday life but mostly done automatically and requires less or no end-user interaction. The majority of the devices connected to the internet (SHOULD*) have some form of encryption capabilities activated if data/information is being transferred or exchanged…which is almost the case in every scenario.
What I am saying is that encryption capabilities are mainly highly abstracted. This makes the subject also a bit harder to grasp from an end-user perspective but on the other hand, it makes it more end-user friendly from an experience perspective.
Below are some common examples and scenarios I have used throughout my career to explain the Integrity perspective and how damage to the Integrity perspective may be caused.
Note*: IoT (Internet of Things), OT (Operational Technology), and legacy systems for example do not always carry these capabilities, i.e. encryption.
INTEGRITY EXAMPLES
Medical industry
For an organization operating in the medical industry producing digital information related to the ingredients for their medicines will have strong requirements to ensure the accuracy of the data and information is correct. A “0” can potentially cause detrimental negative effects or if the ingredients are not accurate and complete. For example, the implications of dosage or ingredients in medicine changing to 100 mg instead of 10 mg. The dosage is amplified with a factor of 10 due to that extra “0”.
Financial industry
An organization operating in the financial industry conducting several millions of digital monetary transactions daily will strongly rely on the accuracy of the data and information. If the correctness of the transaction sum or receiving account information is not ensured to be correct this can have a huge negative financial impact. As millions of transactions are made every day even the smallest changes in decimals may cause severe damage to the organization from a financial and monetary perspective if the Integrity of data/information is damaged.
The universal nature of the CIA triad provides wide coverage of scenarios for where the model can be applied and used within security. Personally, I like the CIA triad just because of this reason. It is a universal tool.
PRACTICAL USAGE OF THE CIA TRIAD
The perspectives speak about security in terms of something that everyone more or less can relate to. Scenarios are easy to craft around each perspective of the triad and analogies are simple to develop. And as mentioned before, the tool is universal which means it can be used very widely. I will give a very good scenario where the CIA triad fits in perfectly from a security perspective.
CLASSIFICATION & CATEGORIZATION
The CIA triad is commonly seen as an applied tool in the classification and categorization of assets, i.e. data, information, or systems. The purpose to classify and categorize assets is to identify how these assets shall be adequately protected. The perspectives from the CIA triad can together with metrics (between 1 – 4 for example) be used to form a matrix consisting of information labels to guide the classification and categorization of the assets.
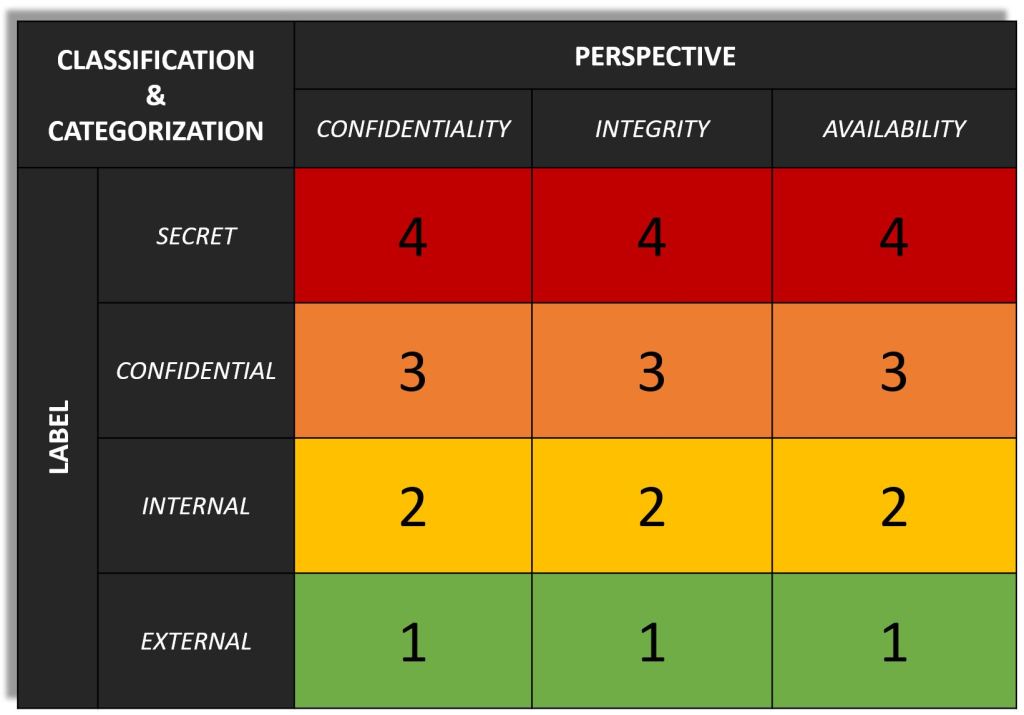
This method is commonly used within the discipline called Information Classification. Each perspective applied in the matrix is used to assess and classify the value of the information for the organization. This will provide the information owner in the organization with an understanding of the potential consequences, requirements, and risks. The classification of the information serves the information owner, with the help of the IT organization, to determine what form of protection is needed.
All assets within an organization are not, and shall not be treated as, equally critical, or sensitive. Generally, few assets are highly critical and sensitive for an organization, and it is these that need more protection. The most critical and sensitive assets shall be protected with adequate protective measures in relation to their value to the organization.
If more protection is applied this also, means a higher cost. The increased cost can be a result of additional security controls applied to fulfill the required security level in relation to the value of the asset. And it may also result in a slightly higher administrative overhead, i.e. if the security controls in place make it harder for the end user to accomplish their task. If more security controls are applied this should also equate to that the security is harder to be breached by an adversarial threat actor.
Information classification is a subject of its own that I will cover in future articles so for now, I will stop here for now. I think you get the understanding and potential practical usage of the CIA triad and how it can be and is used when it comes to information classification.
RECOMMENDATIONS
The CIA triad is a universal tool, do not limit yourself or your organization to only specific situations and tasks where it can be used.
Use the CIA triad as a tool to communicate around and about security in universal terms. The perspectives can be, almost, applied everywhere. Use your fantasy and imagination and create those stories.
Use the CIA triad as a fundamental tool when information classification and systems categorization is conducted. This will help to guide the classification and categorization exercise.
FOR YOUR INFORMATION
If you who read this article came this far, I think you might be interested in this article:
SAFEGUARDING THE CROWN JEWELS – INFORMATION CLASSIFICATION
Henrik Parkkinen