About 40 million lightning strikes hit the ground in the United States each year. But the odds of being struck by lightning in a given year are less than one in a million, and almost 90% of all lightning strike victims survive. The odds of being struck multiple times is even less, with the record being seven times in one lifetime. There are some factors that can put you at greater risk of being struck, such as participating in outdoor recreational activities or working outside. Regional and seasonal differences can also affect your risk of being struck by lightning.
Center for Disease Control and Prevention
Lightning is pretty damn cool! I think there is something highly fascinating when nature manifests its power. <SCCHKBAAAAAAM!!!> And the lightning flashes down from the sky and spreads like a gigantic tree of pure light. Electrifying!
In Norse mythology, it was said thunders and lightning were an act of the war god Tor when he swung and slammed his hammer, Mjolnir. With the help of science, we now know that this is not the case. It is not a gigantic über jacked dude with long blond hair, blue eyes, awesome beard, and masculine as no other who does some cool things in the sky with a large hammer.

The short answer to “What is lightning?” is An electrical discharge caused by imbalances between storm clouds and the ground, or within the clouds themselves. The Tor dude sounds a bit cooler I must say. Don’t you agree?
Enough about Lightning, thunder, and Viking gods. Today’s article is about risk. Not the risk related to that “less than one in a million risk of being hit by lightning”. Today’s article is about risk in the context of security.
When I say security, I referred to Cyber Security, Information Security, and IT security. I put these things in the same bucket due to that they interrelate with each other. And each of these three disciplines serves the same purpose. But more about that in another article. Let’s stick to explaining “Risk” now.
WHAT IS RISK?
As described in my article named What Is Risk Management, I explained “risk” in the context of security as something negative. Below is an extract from that article.
“The term risk when it comes to security is related to something negative. Risk is not generally something that is negative though but, in this article, and for most scenarios when it comes to security related to cyber, information, and IT security it is something negative. […]”
In this article, I will zoom in on the term “risk” and explain it with the help of a model. I am a strong believer in modelizing explanations in visuals as this makes it easier for our brains to pick up on abstract concepts, such as theories, methodologies, processes, and so forth.
And yes, there are other models out there that can be used to model risk. I am not arguing against those. This article serves as a contribution, to how risk in the context of security can be modeled and made easy to understand. The model has served me well during my career in explaining “security risk” to organizations and individuals.
“Amazing and brilliant! This model made things much more easier to understand Henrik! Great explanation and a great visualization of security risk!”
N N, Automotive Industry
Let’s jump in! You who are familiar with publications from NIST, ISO, ISACA, and other well-known standards and frameworks will find similarities.
DESCRIPTIONS OF RISK
In my article What is Risk Management, I described “Risk” with the help of three descriptions.
Description #1
The summary of the combined impact and likelihood of a negative event occurring.
Description #2
A threat exploiting a vulnerability that is resulting in negative damage to an asset.
Description #3
A Risk is the summary of the combined impact and likelihood of a threat exploiting a vulnerability that is resulting in negative damage to an asset.
My personal favorite is Description #3, as this description gives a good summary and explanation of what a risk consists of in the context of security. Below is a short description of each term.
- Impact – The magnitude of the negative event from a threat exploiting a vulnerability.
- Likelihood – The probability of something, i.e. an event, happening.
- Asset – Something of either tangible or intangible value that is work protecting. For example, humans, data, information, intellectual properties, reputation, business processes, and finances.
- Threat – A potential cause of an unwanted incident or anything that is capable of acting against an asset in a manner that can result in a negative impact or consequence. A threat is in general something that cannot be controlled. For example, a hurricane, geo-political events, or cybercriminals. When there is a human behind a threat, they are in most cases driven by two factors: skill and motivation. Skill is the knowledge they possess. Motivation is in most cases related to financial and monetary aspects.
- Vulnerability – a weakness in the design, implementation, operation, or internal control of an asset (system, process, infrastructure, human) that could expose the asset to adverse threats or threat events. A vulnerability is in general something that can be controlled, i.e. mitigated. For example, a security update is missing on a system, a bug is identified in the software, and the employees lack security awareness training.
- Risk – see explanation above.
I will provide a model for Description #3 where I will illustrate the interrelationship of the terms of risk in the context of security.
RISK MODELIZED
A risk exists in a context, it does not operate in a vacuum. In the model, I will present, risk is the function of a threat, vulnerability, asset, likelihood, and impact. See Figure 1 below.
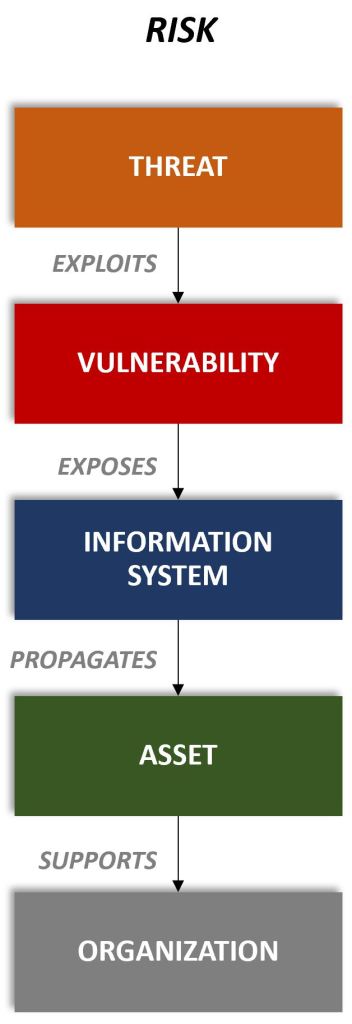
In Figure 1 there are two new terms mentioned that I did not explain above. These are Information System and Organization.
To exemplify them in the model let us assume an external adversarial Threat actor, i.e. cyber criminal, exploits a vulnerability in an information system. The vulnerability exposes the information system and propagates the exposure to its Asset(s).
The Asset(s) are supporting the Organization to for example provide services to internal and external stakeholders. The Asset(s) also play a vital role in the organization to achieve its vision, mission, and objectives. The Asset(s) could for example be business-critical intellectual properties, patents, services provided to external customers, PII, and so forth. These are examples. The model is applicable to non-business critical and sensitive asset as well.
For an organization to protect the information systems and related assets they need to apply and implement adequate counters measures, i.e. security controls. The security controls need to reflect the requirements of the organization, information system, and asset(s) to reduce the risk(s) to an acceptable level.
Security control(s) are countermeasures to identify, protect, detect, respond or recover from a security threat, risk, event or incident. Security control(s) can be Administrative (Managerial), Technical (Logical), Operational (Procedural), or Physical and applied automatically or manually. Figure 2 illustrates the relationship of security controls to the attributes that risk consists of.
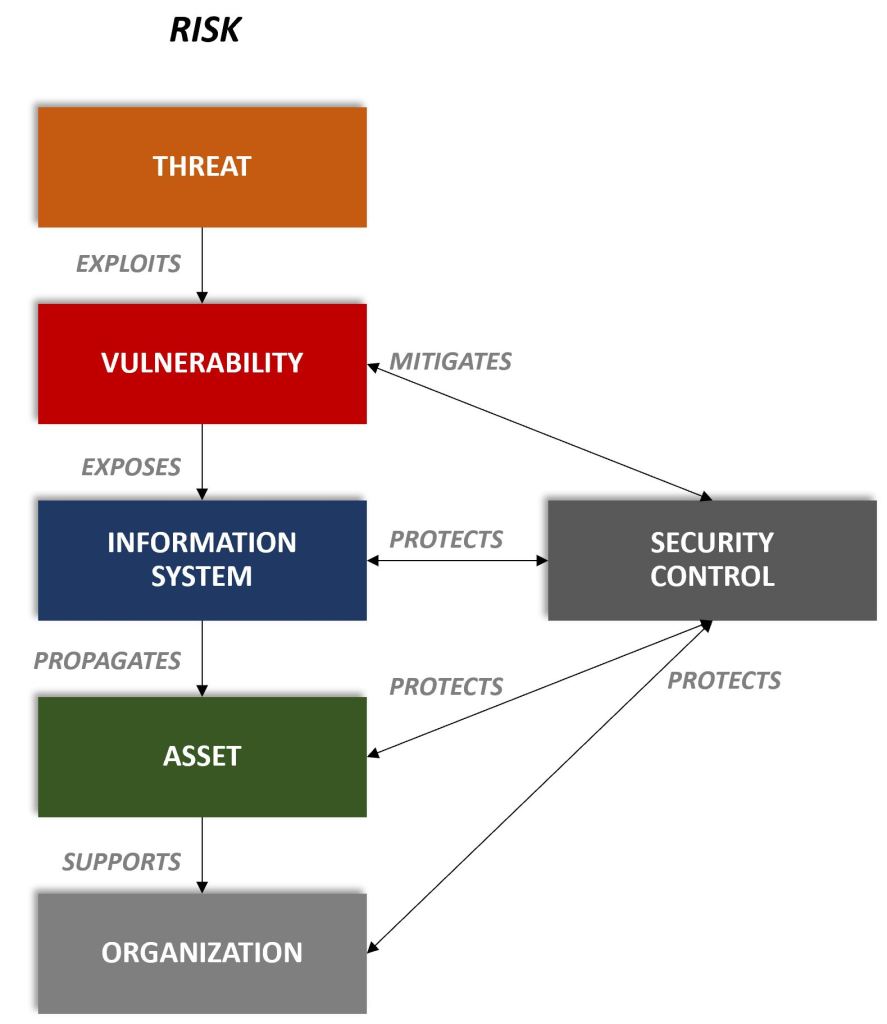
Figure 2 illustrates how a Security Control, in the modelized security risk, mitigates a vulnerability and protects the information system, asset, and organization. The security controls provide protection against Threats by the inheritance through the implementation to mitigate the vulnerabilities that a Threat exploits.
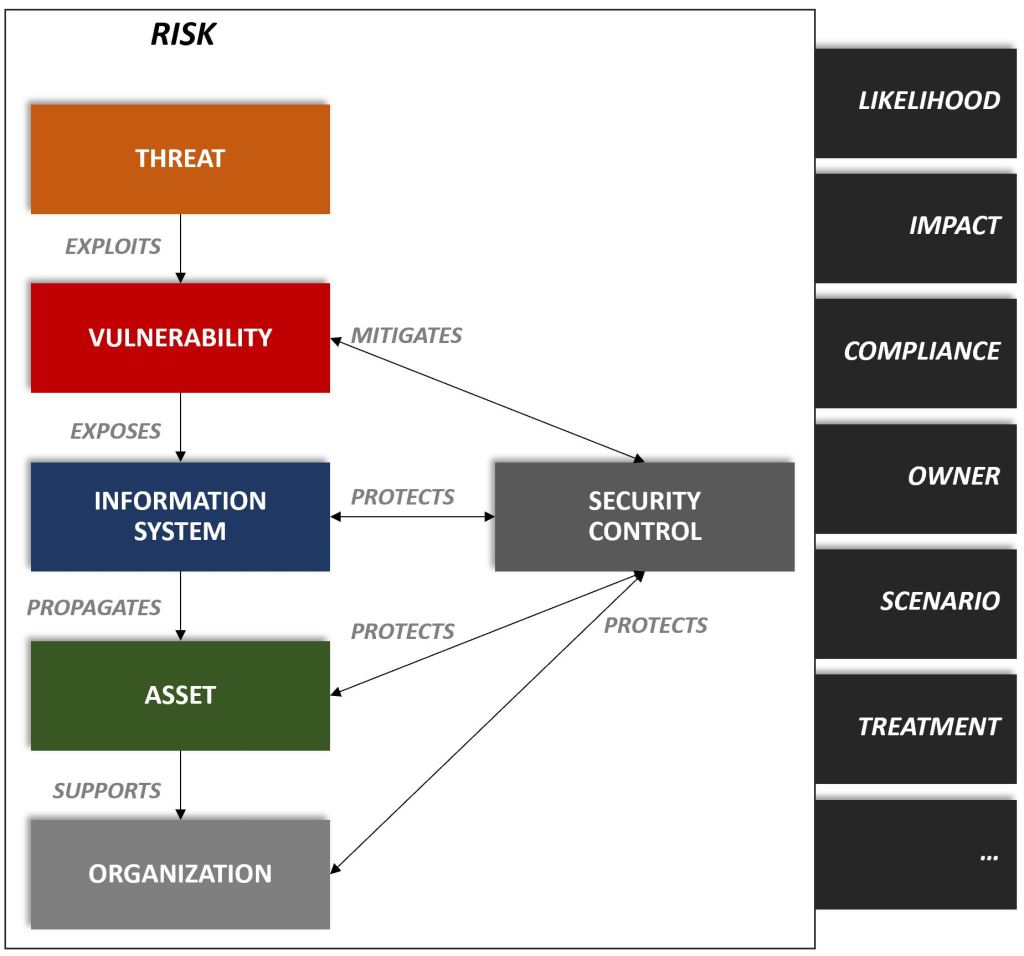
As mentioned earlier in this article, a risk contains the attributes “Likelihood” and “Impact” the terms that I described above. But these are not the only attributes that a Risk consists of. On the right side in Figure 3 below, and as described in my other articles about Risk Management and the Risk Assessment process, I present those other attributes that are related to risk.
security incident, EVENT & RISK
Risk does not exist in a vacuum. Risk exists in a context. And for an organization to stay secure and protected security risks need to be managed and operated continually from an operational, tactical, and strategic perspective.
The reason for this is due to that risk in the context of security is dynamic. They change over time, and so do some of the attributes within a risk. For example a Threat. The wake-away message: Risks within the context of security are not static.
Risk management and Risk assessment are strongly correlated with security incident management. The reason for this is due to that security incident management provides strong operational, tactical, and strategic capabilities for an organization to manage security risk. Figure 4 illustrates the relationship of risk to security incident management.
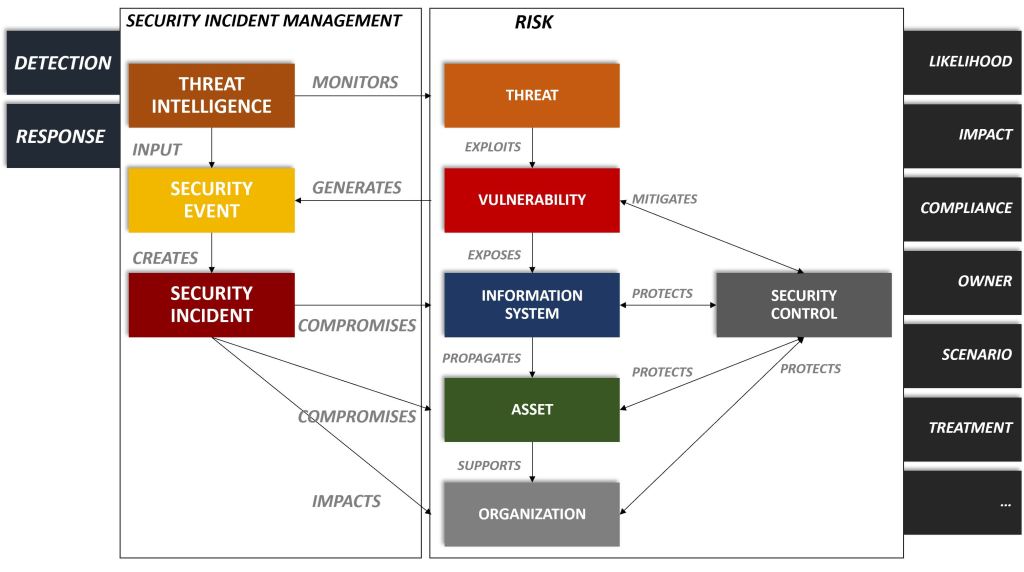
Threats, external and internal, targeted towards an organization are monitored with the help of Threat Intelligence. Threat intelligence provides intel to the organization that can be used to craft actionable and applicable countermeasures for the organization against its threats.
Threat Intelligence is used as input to security events that are generated from vulnerabilities. A positive security event creates a security incident, which signals that the information system, asset, and organization has been compromised and impacted.
Two fundamental capabilities for achieving predictive, proactive, and responsive security incident management are Detection and Response management. These two capabilities are visualized on the left side of Figure 4.
Detection management provides capabilities to in timely manner detect anomalies and abnormal patterns. With the help of Response management, an organization can effectively respond, in a timely manner, with adequate actions when anomalies and abnormal patterns are detected.
These types of actions and capabilities usually exist within a SOC, i.e. Security Operations Center. There is of course very much more to be said about the subjects of security incident management, detection, and response management but that I will save for a separate article.
RECOMMENDATIONS
Establish a common understanding of Risk in your organization. Make sure those stakeholders who work with risk in the context of security share the same point of view.
Create a visual model to explain “Risk”. Our brains better understand abstract concepts, theories, methodologies etcetera that are visualized.
Have patience. Communicate and repeat the message. Listen to your stakeholders. Explain to them and engage with them. Security is a team sport. It may take time for others to understand what Risk is within the context of security. And why it is important.
For your information
If you found this article interesting and want to read more about risk management I recommend you to check out these articles:
- What is Risk Management?
- The Risk Assessment Process & Identification Phase Explained
- The Risk Analysis Phase Explained
Henrik Parkkinen